Call SMS Bombers : the ease of connecting with others has brought about both positive and negative aspects. One of the darker sides of this convenience is the emergence of Call SMS Bombers, individuals or groups who exploit communication channels to harass, annoy, or disrupt the lives of unsuspecting victims. we’ll delve into the workings of these mischief-makers, the potential harm they cause, and the measures taken to expose and prevent their activities.
What Are Call SMS Bombers
In the era of smartphones and instant messaging, staying connected with friends and family has never been easier. However, not all aspects of digital communication are as positive as sharing funny memes or sending heartfelt messages. There’s a dark side to this convenience, and it comes in the form of Call SMS Bombers. But what exactly are these digital troublemakers, and why should we be aware of them?
Defining Call SMS Bombers
Let’s start with the basics. Call SMS Bombers are individuals who use technology to flood someone’s phone with an overwhelming number of calls or text messages. It’s like being caught in a digital storm of never-ending buzzes and rings. The people behind these pranks (or sometimes, more malicious actions) use automated tools – like computer programs or apps – to send an unusually large volume of calls or texts to a particular phone number.
Why Do They Do It?
Now, you might be wondering why anyone would bother bombarding someone with calls or texts. Well, the motives can vary. Sometimes, it’s just for fun – a kind of digital prank. Picture it like the classic prank call but on a much larger scale. Other times, however, it can be more serious. Some individuals use these techniques for revenge or harassment, causing a lot of stress and disruption for the person on the receiving end.
How Does It Work?
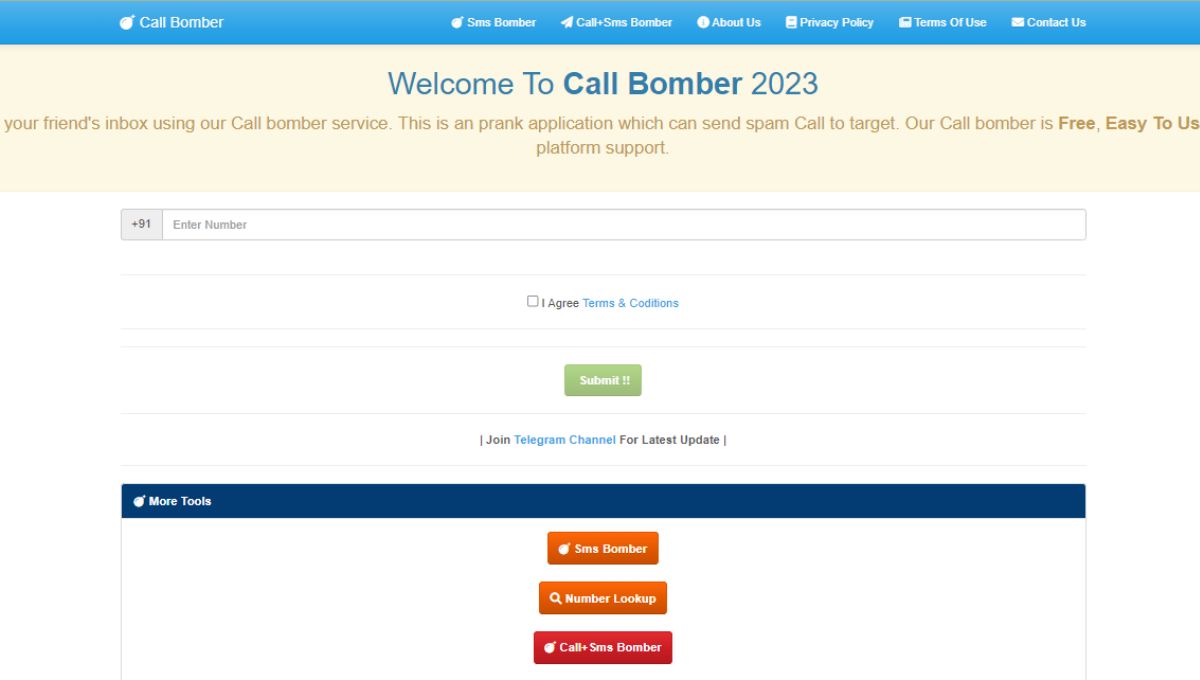
You might be curious about how these digital pranks are pulled off. Call SMS Bombers often use online platforms or apps that provide automated calling or messaging services. While these services are meant for legitimate purposes, some people misuse them for their own amusement or to cause harm. It’s like someone taking a tool that’s meant for building something good and using it to create chaos instead.
Additionally, some bombers use multiple SIM cards or virtual phone numbers to make it harder to trace them. Imagine trying to catch someone who wears a different disguise every time they play a prank – it’s not an easy task!
The Impact on Victims
Now, let’s talk about the real-life impact on those who fall victim to these digital storms. Imagine your phone buzzing or ringing incessantly, receiving call after call or message after message. It’s not just annoying; it can be seriously stressful. Victims can find it hard to focus on work or studies, and the constant disturbance can affect their mental well-being.
In more serious cases, call and SMS bombing can even interfere with emergency services. Imagine needing help urgently and not being able to get through because your phone is tied up with spam calls. It’s not just an annoyance anymore; it’s a potential danger.
The Cat-and-Mouse Game: Catching the Culprits
So, what’s being done to stop these digital pranksters? It turns out there’s a kind of cat-and-mouse game happening between the bombers and those trying to stop them. Here are some strategies being used:
- Pattern Recognition: Experts are developing smart computer programs that can recognize unusual patterns associated with SMS and call bombing. If they notice something fishy, they can act quickly to stop the bombardment.
- Teamwork with Service Providers: Collaboration is key. Authorities work closely with phone companies to track down and block numbers linked to bombing activities. It’s like a digital neighborhood watch, with everyone working together to keep things safe.
- Educating Users: Knowledge is power. By teaching people about the risks of using automated calling and messaging services for pranks or more harmful activities, there’s hope that individuals will think twice before engaging in such behavior.
- Laws and Penalties: There are consequences for those caught engaging in call and SMS bombing. Strict laws and penalties serve as a deterrent, making potential offenders think twice about causing digital mayhem.
Real Stories, Real People
To truly understand the impact of call and SMS bombing, we need to look beyond the technical details and statistics. Let’s take a moment to consider real stories from real people who have been targeted. Imagine being in Sarah’s shoes – a college student whose studies were disrupted and whose peace of mind was shattered by a relentless stream of messages. These stories highlight the human side of the issue and emphasize the need for action.
Balancing Act: Privacy vs. Security
As we try to address the problem of call and SMS bombing, we run into an ethical dilemma – how do we balance privacy and security? It’s crucial to protect individuals from harassment, but it’s just as important to respect privacy rights. Striking the right balance means finding ways to stop the bombers without infringing on the rights of innocent individuals.
This delicate dance involves collaboration between lawmakers, technologists, and the public. Together, they must create guidelines that effectively address the issue without compromising individual privacy. It’s like walking a tightrope, requiring careful consideration and thoughtful decisions.
Looking to the Future: A Safer Digital Landscape
In the ever-evolving world of digital communication, the fight against Call SMS Bombers continues. With advancements in technology and collective efforts from various stakeholders, there’s hope for a safer and more secure digital future. Raising awareness, implementing preventive measures, and holding perpetrators accountable are all steps in the right direction.
The Harrowing Impact on Victims
Imagine receiving hundreds of calls or messages in a matter of minutes, causing your phone to constantly ring or vibrate. This relentless barrage can be overwhelming, leading to increased stress, anxiety, and disruption of daily activities. Victims may find it difficult to focus at work or school, and the invasion of privacy can take a toll on their mental well-being.
In extreme cases, SMS and call bombing can have serious consequences, such as interfering with emergency services. If a victim’s phone is constantly tied up with spam calls or messages, they may be unable to make or receive important calls, including those to emergency services. This potential for real-world harm underscores the importance of addressing and preventing such activities.
How Call SMS Bombers Operate
In the world of smartphones and instant messaging, connecting with friends and family is a breeze. However, there’s a shadowy side to this convenience – enter Call SMS Bombers, the mischief-makers of the digital world. But how exactly do these digital pranksters operate? Let’s take a peek behind the scenes and uncover the workings of call and SMS bombing.
Automated Tools: The Bomber’s Best Friends
At the heart of call and SMS bombing operations are automated tools. Imagine having a robot friend who can make countless calls or send a barrage of text messages in the blink of an eye. These tools, often in the form of computer programs or apps, allow bombers to carry out their pranks on a massive scale without manually dialing each number or typing out every message.
Online Platforms: A Playground for Pranks
Where do bombers get these automated tools? Many of them turn to online platforms that offer services intended for legitimate purposes. These platforms might provide automated calling or messaging services for businesses or organizations to reach their customers more efficiently. Unfortunately, some mischief-makers misuse these tools for their own amusement or, in more serious cases, to cause harm.
Multiple Identities: Playing Hide and Seek
Bombers don’t want to get caught, so they often play a game of hide and seek with authorities. One trick up their sleeves is the use of multiple identities. They might use different SIM cards or virtual phone numbers, making it challenging for investigators to trace them. It’s like wearing disguises – each time they strike, it’s with a new identity.
Why Do They Do It? The Motives Behind the Mayhem
Understanding why someone would engage in call and SMS bombing is like peeling an onion – there are layers to it. Some do it for the thrill of a digital prank, finding amusement in the chaos they create. Picture it as a mischievous laughter echoing in the digital realm. Others, however, might have more serious motives, like seeking revenge or intentionally causing distress to someone they know. It’s a digital form of playing with fire, with potential consequences ranging from annoyance to real harm.
The Anonymity Factor: A Digital Mask
Anonymity is like a digital mask that bombers wear to shield themselves from consequences. By using multiple identities and virtual phone numbers, they create a layer of separation between their actions and their real-life selves. This digital mask makes it difficult for authorities to identify and apprehend them, adding a level of challenge to the efforts to stop their activities.
Evading Detection: The Cat-and-Mouse Game
Once the bombers launch their digital pranks, the game of cat and mouse begins. Authorities and technology experts work tirelessly to catch them, employing strategies like pattern recognition. This involves developing smart algorithms that can detect unusual patterns associated with call and SMS bombing. It’s like setting up digital traps to catch the mischievous digital mice.
Collaboration with Service Providers: Uniting Against Bombers
Stopping Call SMS Bombers requires teamwork, and service providers play a crucial role in this effort. Collaboration between authorities and telecommunications companies is like a neighborhood watch program in the digital world. By working together, they can track down and block numbers associated with bombing activities, putting a halt to the mischief.
The Game of Prevention: Educating Users
One way to curb call and SMS bombing is by preventing it in the first place. This involves educating users about the risks associated with automated calling and messaging services. By spreading awareness about the potential consequences of engaging in these activities, individuals are less likely to become unwitting players in the game of digital pranks.
Efforts to Expose and Prevent Bombers
Law enforcement agencies, technology companies, and cybersecurity experts are actively engaged in a constant battle against Call SMS Bombers. Various measures are taken to identify, expose, and prevent these malicious activities. Some of these include:
- Pattern Recognition: Developing sophisticated algorithms that can recognize patterns associated with SMS and call bombing. By analyzing data and identifying unusual patterns of activity, authorities can pinpoint potential bombers and take appropriate action.
- Collaboration with Service Providers: Working closely with telecommunications service providers to track and block numbers associated with bombing activities. This collaboration helps in quickly shutting down the channels used by bombers to carry out their attacks.
- User Education: Educating users about the risks of using automated calling and messaging services for malicious purposes. By raising awareness about the potential consequences of such actions, individuals are less likely to engage in or support call and SMS bombing.
- Legislation and Penalties: Implementing and enforcing strict laws against call and SMS bombing. Legal consequences serve as a deterrent for potential offenders and provide a framework for prosecuting those caught engaging in such activities.
Real Stories Behind the Numbers
To truly understand the impact of call and SMS bombing, it’s essential to look beyond the statistics and delve into the real stories of victims. Many individuals have faced the harrowing experience of being targeted by bombers, and their stories serve as a stark reminder of the human cost associated with these malicious activities.
Take the case of Sarah, a college student who became the target of an SMS bombing campaign. The constant barrage of messages not only disrupted her studies but also led to increased anxiety and fear for her safety. Sarah’s story is just one of many, highlighting the need for collective efforts to combat this form of digital harassment.
Balancing Privacy and Security
As technology advances, the ethical implications of addressing call and SMS bombing become more complex. While it is crucial to protect individuals from harassment and potential harm, it is equally important to safeguard privacy rights. Striking the right balance between security measures and respecting individual privacy is an ongoing challenge that requires careful consideration.
Lawmakers, technologists, and the public must work together to establish guidelines that address the issue effectively without infringing on the rights of innocent individuals. This delicate balance is essential in creating a secure digital environment that promotes responsible communication while protecting against malicious activities.
A Safer Digital Future
As we navigate the evolving landscape of digital communication, the battle against Call SMS Bombers continues. Technological advancements, coupled with collaborative efforts between stakeholders, offer hope for a safer and more secure digital future. By raising awareness, implementing effective preventive measures, and holding perpetrators accountable, we can collectively work towards mitigating the impact of call and SMS bombing on individuals and society as a whole.
Conclusion
Call SMS Bombers represent a concerning aspect of our interconnected world. However, through understanding, awareness, and concerted efforts, we can strive to create an environment where the benefits of digital communication are harnessed responsibly, without compromising the safety and well-being of individuals.